Cyber Security

Cyber security
Cyber Security Management Committee
- According to Article 38-1 of "Implementation Rules of Internal Audit and Internal Control System of Financial Holding Companies and Banking Industries", a person above Executive Vice President or with equivalent responsibilities shall be designated as CISO. In 2011, the Executive Vice President who supervised the Information Security Dept. served as the CISO to enhance the Bank's ability to implement information security issues.
- The Bank has established the "Cyber Security Management Committee" to effectively implement matters related to cyber security management. The committee is chaired by the Chief Information Security Officer, who oversees the execution and coordination of cyber security management matters. During meetings, Board member Xin-Wu Lin and Jin-Long Liu attend to Cyber Security Management Committee and provide suggestions. They also review the implementation of the Bank’s overall cyber security management. Cyber Security Management Committee also invites cybersecurity consulting experts to attend and offer professional opinions when discussing significant cybersecurity issues. They provide professional opinions on proposals regarding significant cybersecurity issues and receive consultation from the Board of Directors. The Cyber Security Management Committee convened 11 times in 2024.
- The establishment of the Cyber Security Management Committee shows the Bank's emphasis on cyber security, so that cyber security is no longer a slogan, but the implementation of the system.
Cyber Security Management Policy
- To ensure the security of the Bank’s information and communication systems and information assets, strengthen the overall cyber security framework, and mitigate operational risks, the Bank has established the “Cyber Security Management Policy.” The policy aims to prevent unauthorized access, use, control, disclosure, destruction, alteration, loss, or other infringements, thereby ensuring the confidentiality, integrity, and availability of information assets. The Bank continues to enhance its cyber security defense mechanisms in accordance with the annual Cyber Security Maintenance Program.
- To ensure the continuous operation of its information and communication systems, the Bank has established a Cyber Security Maintenance Program and a Cyber Security Incident Response Mechanism, and conducts regular incident response drills. In addition, the Bank has implemented cyber security threat monitoring and response measures to enable early detection and mitigation, thereby reducing potential impacts. In the event of a cyber security incident, the Bank will handle the incident in accordance with its cyber security incident reporting procedures and major incident management mechanisms, and will proactively communicate incident handling status and subsequent improvement measures to affected stakeholders, based on the nature and impact of the incident.
- All employees, suppliers, and visitors of the Bank are required to comply with the Cyber Security Management Policy. Suppliers cooperating with the Bank shall adhere to the cyber security requirements set out in the “Cyber Security Terms and Agreements.” Bank employees have the responsibility and obligation to protect the information assets under their use. Personnel demonstrating outstanding performance or causing losses to the Bank in the course of handling cyber security–related matters shall be subject to rewards, penalties, or performance evaluations in accordance with the Bank’s relevant policies, depending on the severity of the circumstances.
- The Bank reviews its Cyber Security Management Policy annually or re-evaluates it when material changes occur. In addition, the Bank engages an independent third-party institution to assess the effectiveness of the overall cyber security implementation each year. The overall cyber security implementation status for the preceding year is reported to the Board of Directors in the first quarter of each year.

Risk management framework
- To ensure the effective implementation of information and communication security operations, the Bank adopts the Three Lines of Defense model to define clear responsibilities and maintain a robust security framework. The first line of defense comprises the Bank’s I&C system management and user departments, responsible for the design and execution of security controls. The second line of defense is the Information Security Department, which is responsible for the planning and oversight of I&C security management operations. The third line of defense is the Board of Directors’ Audit Office, which performs independent audits to evaluate the effectiveness of I&C security operations, including access control, protective measures, and security incident reporting.
- In order to ensure that the operation process has been adjusted to the most appropriate state, dedicated person will be assigned to take on-the-spot counseling from time to time to assist relevant units to improve cyber security operations as soon as possible.
- Submit the bank's cyber security handling situation to the risk management committee every month, and submit the information security handling situation to the Cyber Security Management Committee for review every quarter, and then submit it to the board of directors for report, so as to improve the board of directors' understanding of the bank's cyber security status.
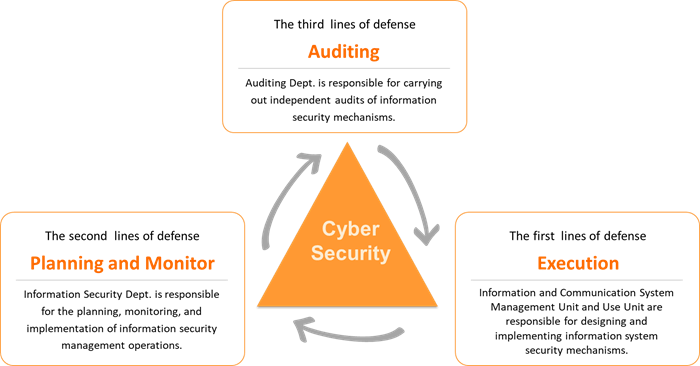
The Bank’s cyber security risk management framework is based on the “Three Lines of Defense.” The first line consists of all system management and user departments, responsible for the design and execution of controls. The second line is the Information Security Department, responsible for planning and overseeing cyber security management operations. The third line is the Audit Department under the Board of Directors, which performs independent audits to evaluate the effectiveness of cyber security operations, including access control, security protection, and incident reporting.
Introduce international cyber security management standards and obtain certification: To ensure the confidentiality, integrity, and availability of customer data and related operational information, the Bank obtained "ISO 27001 Information Security Management System" international standard certification in November 2010 and has maintained the validity of the certificate every year (the certificate is valid until November 6, 2025).
Notification process for cyber security incidents
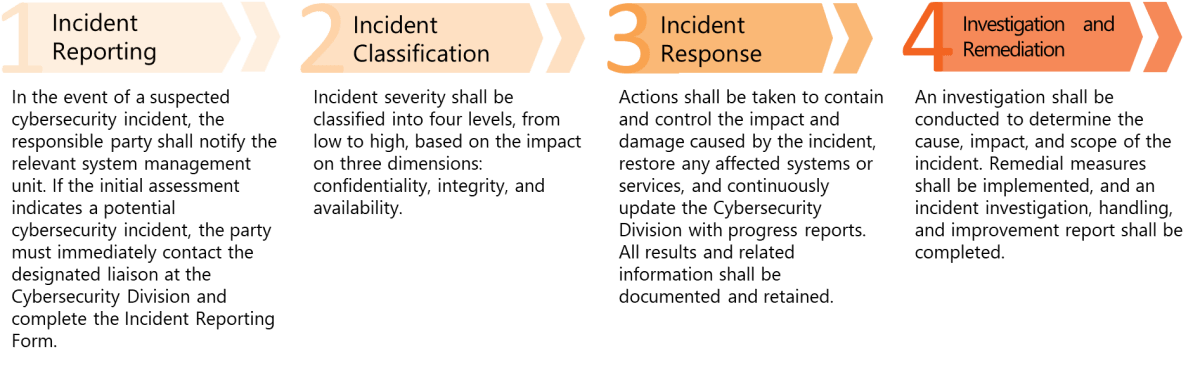
The Bank has established a clear reporting mechanism requiring employees, upon discovering or becoming aware of a potential or actual cyber security incident, to follow the Bank’s incident reporting procedures. They must promptly carry out damage control, recovery, investigation, and remediation. Cyber security incidents are classified and handled based on their severity, and, when necessary, escalated to senior management or competent authorities. All incidents are fully documented and monitored throughout the process to ensure timely risk management and effective response.
Concrete management programs, and investments in resources for cyber security management
- The Information Security Department reports the status of information and communication security (ICS) operations to the Risk Management Committee on a monthly basis. On a quarterly basis, the consolidated implementation status of cybersecurity operations is reported to the Cyber Security Management Committee. Upon review by the Committee, the matters are further submitted to the Audit Committee and the Board of Directors for acknowledgement and approval, thereby strengthening the Board’s oversight and decision‑making with respect to cybersecurity risks. In 2025, a total of 14 meetings were convened, covering topics including quarterly reports on cybersecurity implementation, the Cybersecurity Maintenance Program, and business continuity and resilience drills.
- In response to directives from supervisory authorities, industry associations, and the Bank’s operational requirements, the Bank continuously amends and supplements its internal cybersecurity policies and regulations. In addition, a comprehensive review and inventory of cybersecurity‑related regulations are proactively conducted every fourth quarter. In 2025, a total of 11 cybersecurity regulations were revised or newly enacted, and the Bank’s Cyber Security Policy and Cloud Policy were re‑examined in the fourth quarter to ensure alignment with the latest regulatory requirements, cybersecurity technologies, and business developments.
- In 2025, the Bank completed information security assessments of computer systems, vulnerability scanning of personal computers and business workstations, and security testing of mobile applications (Apps). All identified vulnerabilities were recorded in the Vulnerability Management System (VMS), categorized and managed based on risk severity, with remediation prioritized for high‑risk items, thereby enhancing the security protection of the Bank’s networks and information systems.
- The Bank has established a defense‑in‑depth security architecture encompassing firewalls, web application firewalls (WAF), intrusion prevention systems (IPS), spam filtering, internet usage management, network threat intelligence protection gateways, early warning systems for malicious threats, and endpoint detection and response (EDR) systems. Protection strategies are continuously adjusted in response to evolving threat landscapes to strengthen overall information and communication security.
- To enhance cybersecurity defense and response capabilities, the Bank conducted multiple cybersecurity exercises in 2025, including information security incident reporting and response drills, Distributed Denial of Service (DDoS) attack and defense exercises, and Red Team (ethical hacking) assessments conducted by professional cybersecurity firms to identify potential risks and strengthen defensive readiness. In addition, to enhance employees’ awareness of social engineering threats, the Bank conducted a total of 12 email social engineering simulation exercises for all employees during 2025.
- In addition to being a member of the Financial Information Sharing and Analysis Center (F‑ISAC) and the Taiwan Computer Emergency Response Team / Coordination Center (TWCERT/CC) and actively participating in threat intelligence sharing, the Bank also independently collects cyber threat intelligence from the Hong Kong Computer Emergency Response Team Coordination Centre (HKCERT), internal cybersecurity sources, and external public reports. Dedicated cybersecurity personnel are assigned to receive, analyze, and track remediation progress, enabling the Bank to stay informed of emerging threats and formulate appropriate control and response measures.
- The Bank has established a Security Operations Center (SOC) staffed with professional cybersecurity monitoring personnel. Through a Security Information and Event Management (SIEM) platform, alerts and anomalous activities related to application systems, network devices, endpoint devices, and critical information and communication assets are centrally collected and monitored to promptly detect internal anomalies and external cyber threats. Identified actual or potential risks are handled in accordance with established procedures, including event correlation analysis, alert notification, and response actions, to ensure comprehensive monitoring coverage and effective cybersecurity protection for critical assets.
- Based on job functions, the Bank completed information security awareness training and Internet of Things (IoT) cybersecurity protection courses for all employees in 2025, achieving a 100% completion rate. Each cybersecurity professional completed more than 15 hours of specialized cybersecurity training. In addition, external cybersecurity experts were engaged to provide cybersecurity education and training for directors and senior management.
- The Bank has established information and communication security incident reporting and response procedures, with defined incident severity levels. Root cause analyses are conducted upon completion of incident handling to prevent recurrence. To address the potential impacts of cybersecurity incidents, the Bank has established a Computer Security Incident Response Team (CSIRT), chaired by the Chief Information Security Officer (CISO), to ensure timely incident response and mitigation and to minimize potential damages.
- The Bank has established a Cybersecurity Maintenance Program and an information security incident response mechanism, and conducts regular drills accordingly. In 2025, the Bank conducted business continuity plan exercises for information systems as well as cybersecurity incident reporting and response drills to mitigate the impact of disasters or major incidents on business continuity. In addition, the Bank completed the procurement of Electronic and Computer Crime Comprehensive Insurance to strengthen cybersecurity risk management and mitigate potential financial losses arising from cyber attacks.
- To ensure the confidentiality, integrity, and availability of customer data and the Bank’s operational information, the Bank has implemented and obtained certification under the ISO/IEC 27001 Information Security Management System international standard and maintains the validity of the certification on an annual basis. The current certification is valid until November 6, 2028.
- In 2025, the Bank’s cybersecurity expenditure—including software and hardware licensing fees and personnel training costs—accounted for 13.24% of the total information technology budget.


